
Why CVSS Score Alone Misses the Point of Vulnerability Risk
A CVSS 9.8 with no public exploit is less dangerous than a CVSS 6.5 with a working Metasploit module...
Technical analysis, vulnerability research, and patch management field notes from the PatchGuard team.

A CVSS 9.8 with no public exploit is less dangerous than a CVSS 6.5 with a working Metasploit module...
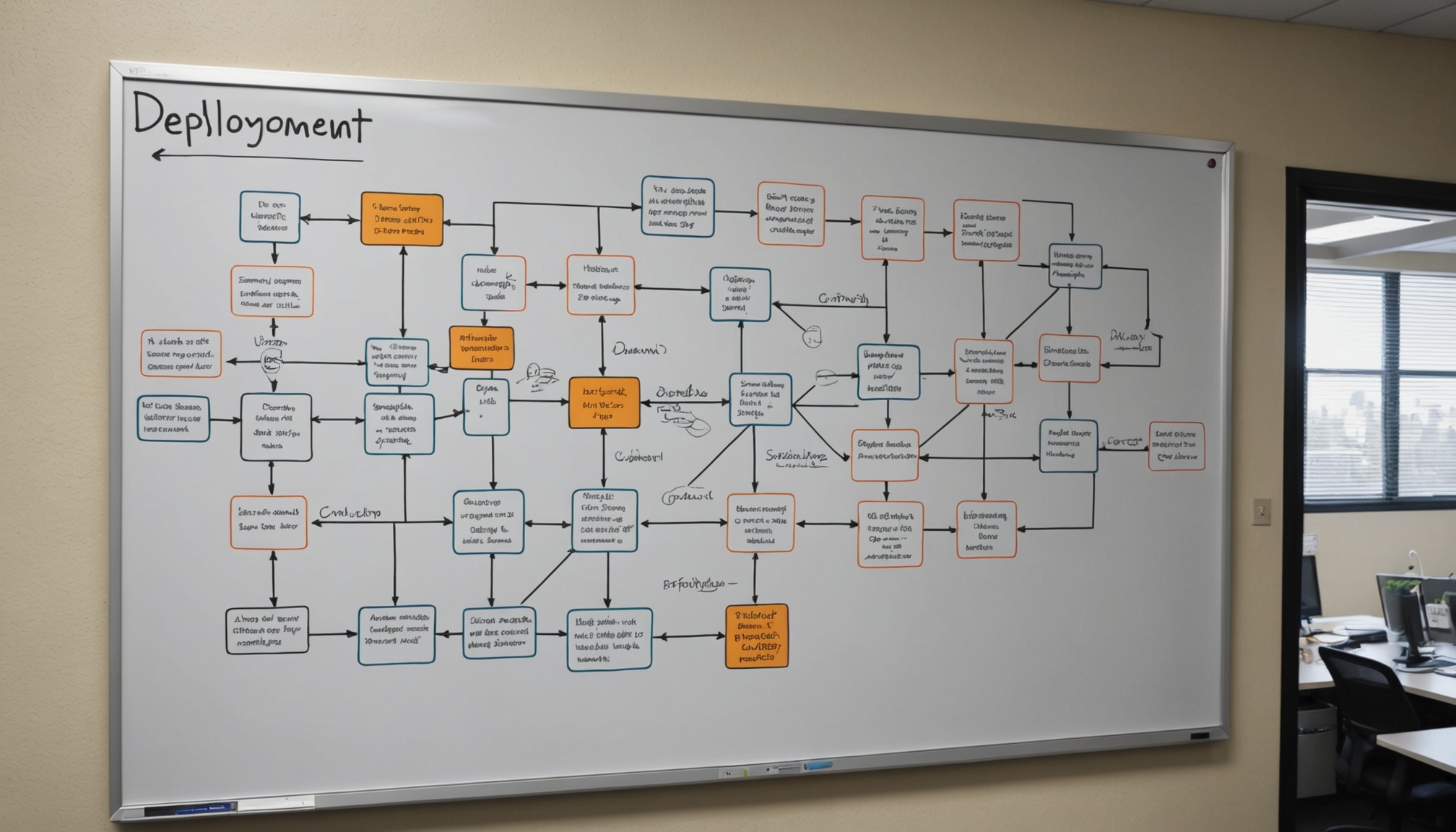
Rolling updates on node pools sound simple until you have stateful workloads and a 4-minute PDB budget...

The Known Exploited Vulnerabilities catalog is authoritative, free, and updated weekly. Most teams treat it as a checkbox...
Building automatic rollback that actually works required us to rethink what a "health check" means post-patch...

Most post-mortems focused on detection speed. The real failure was in orchestrated deployment across heterogeneous environments...

SOC 2 CC7.1 asks for "timely remediation of vulnerabilities." What counts as evidence depends on how you document the process...
Ephemeral containers, auto-scaling groups, and shadow IT turn "what assets do we have" into a genuinely hard operational problem...

WSUS is not enough. WUA returns stale data. And "installed" does not mean "applied." Here's what we've seen in 200+ customer environments...

A 24-hour SLA for critical CVEs sounds reasonable until ops finds out it means patching on Saturday at 2 AM...
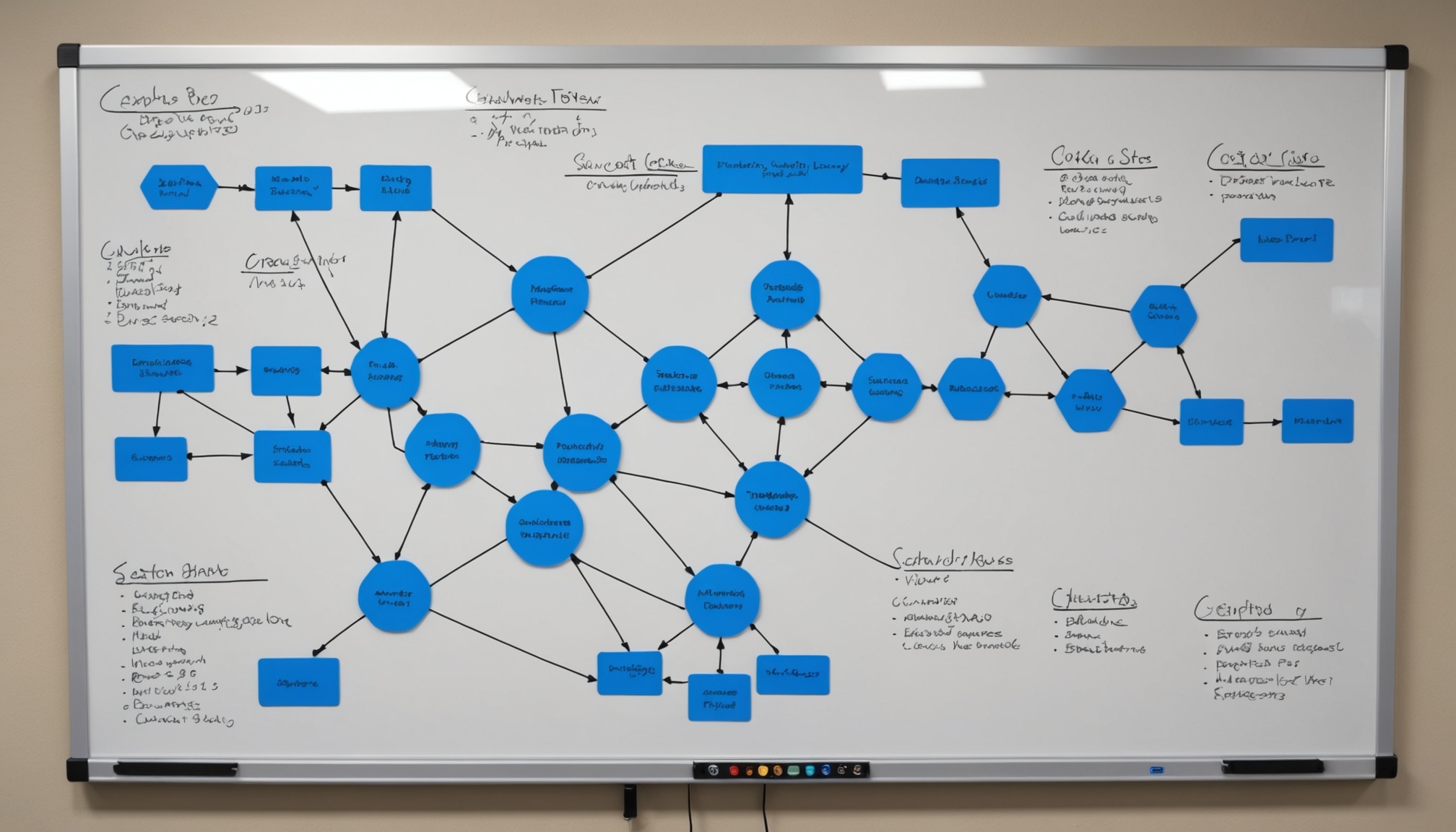
The same risk management principles that protect feature deployments apply directly to patch operations — but almost no security teams use them...

In early 2024, NIST paused NVD enrichment for weeks. If that's your only feed, your scanner is flying blind. Here's how to build redundancy...

The fear of automated patches breaking production is real. The data on manual patching failures is worse. Here's how to frame the trade-off...